Email can be a key piece of evidence in both civil and criminal cases. Yet, as I discussed in my previous post, “Photocopied Text Messages: Don’t Be Fooled by Fabricated Evidence ”, presenting just the visible content of a message is fraught with risk. Fabricated or altered digital evidence can mislead and undermine your case.
Email headers hold the solution to this challenge - they act like a digital fingerprint, revealing information vital for establishing authenticity and the message’s path.
What are Email Headers?
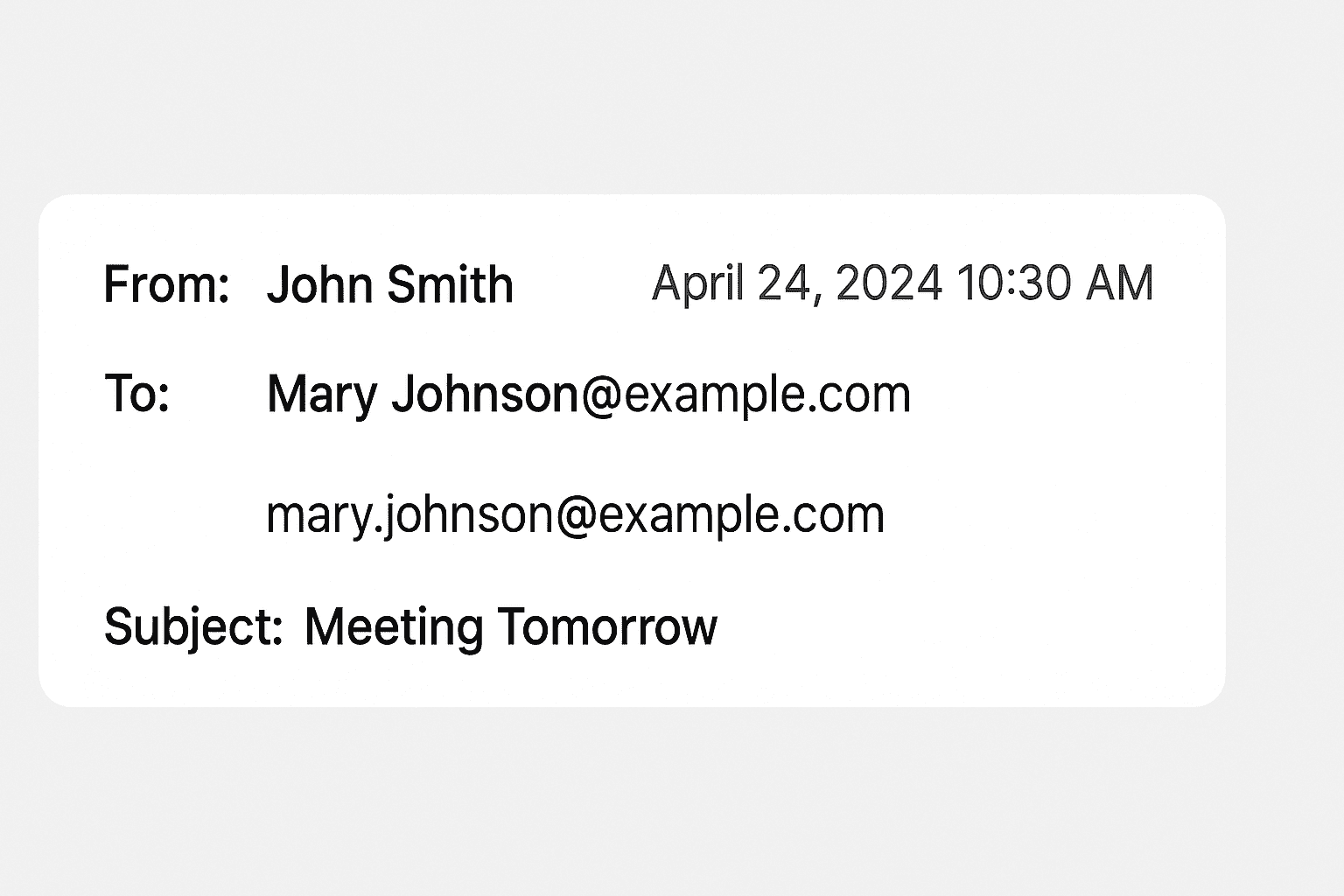
Think of an email as an envelope with a letter inside. The body of the email is the letter’s message; the headers are everything written on the outside of the envelope:
- Sender & Recipient: Not just the visible “From” and “To” fields, but the underlying email addresses and potential routing servers used.
- Timestamps: Detailed dates and times of sending, receiving, and any processing along the way.
- IP Addresses: Network locations indicating where the email originated, and any server hops it took.
- Technical Details: Email client software used, anti-spam checks performed, and more.
Why Email Headers Matter in Court
- Authentication: Headers can establish the true sender of an email. Spoofing the “From” field is easy; however, the IP address and routing data reveal the real origin.
- Timeline: Timestamps in headers help create a precise timeline of events, especially when emails are relayed through multiple servers. This can be crucial in establishing alibis or tracing intent.
- Spotting Alterations: Inconsistencies within the header, or between the header and body content, can expose attempted manipulation.
The Adversarial Challenge
It’s likely the opposing party won’t simply hand over pristine emails with full headers intact. Incomplete or deliberately obscured headers should raise a red flag. Always insist on obtaining, examining, and having a digital forensics expert interpret the complete message, including headers. Lucid Truth Technologies can help you with that.
Don’t Let the Evidence Stop at the Screen
A printout of an email is the digital equivalent of a photocopy, easily tampered with. Email headers give you the tools to authenticate or challenge evidence, protecting your client’s interests. The clues are there, hidden in plain sight – make sure you uncover them.