The Lucid Truth Blog
All
Ai
Audio and video forensics
Background checks and investigations
Cybersecurity and defense
Digital devices in civil litigation
Digital evidence and data recovery
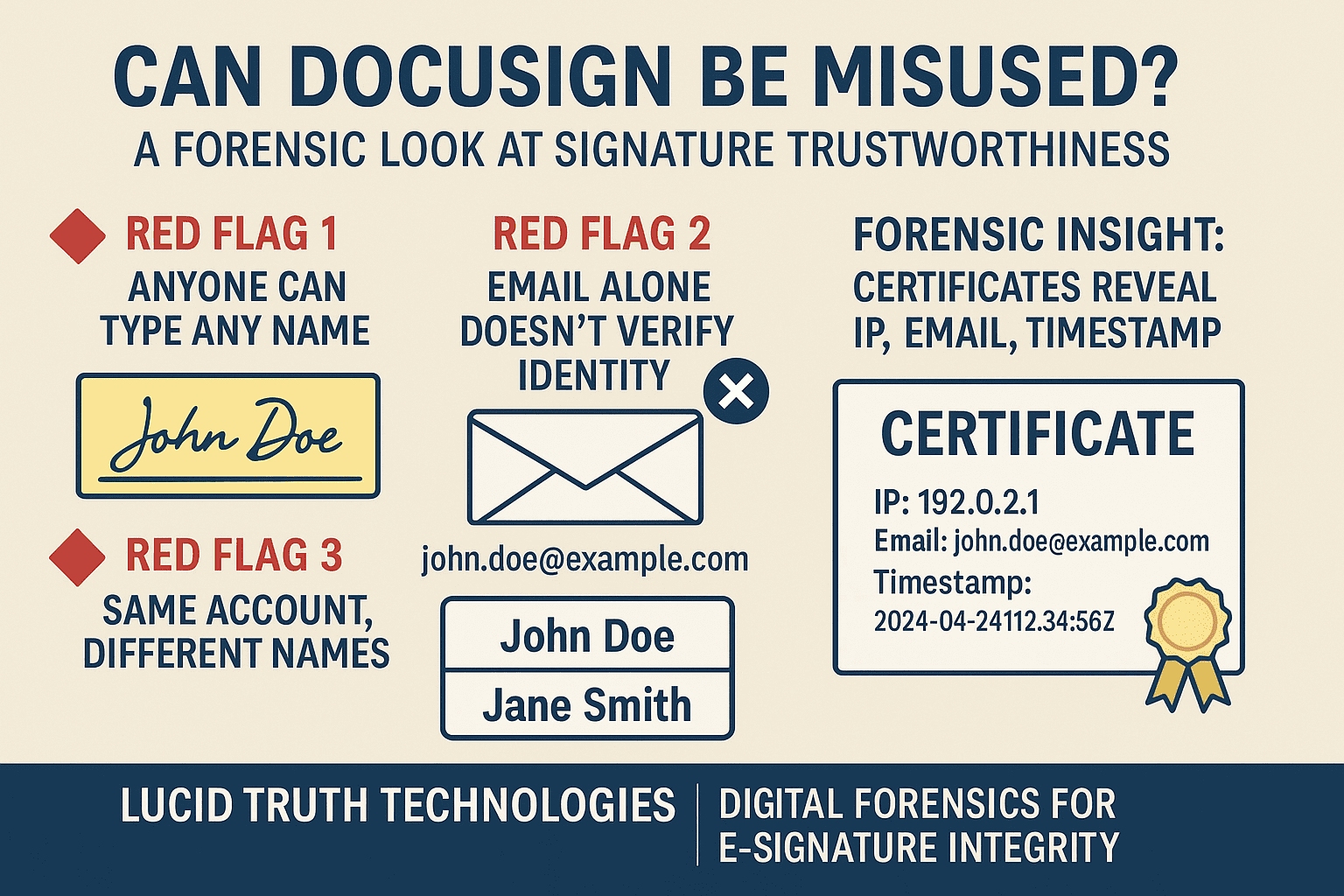
Document forensics
Legal discovery
Legal strategy
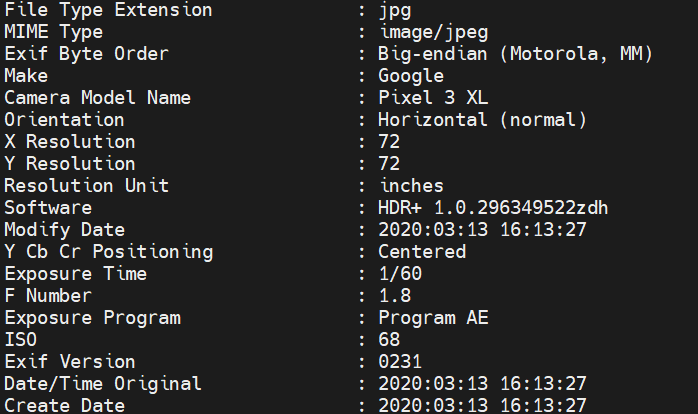
Metadata and data analysis
Mobile forensics
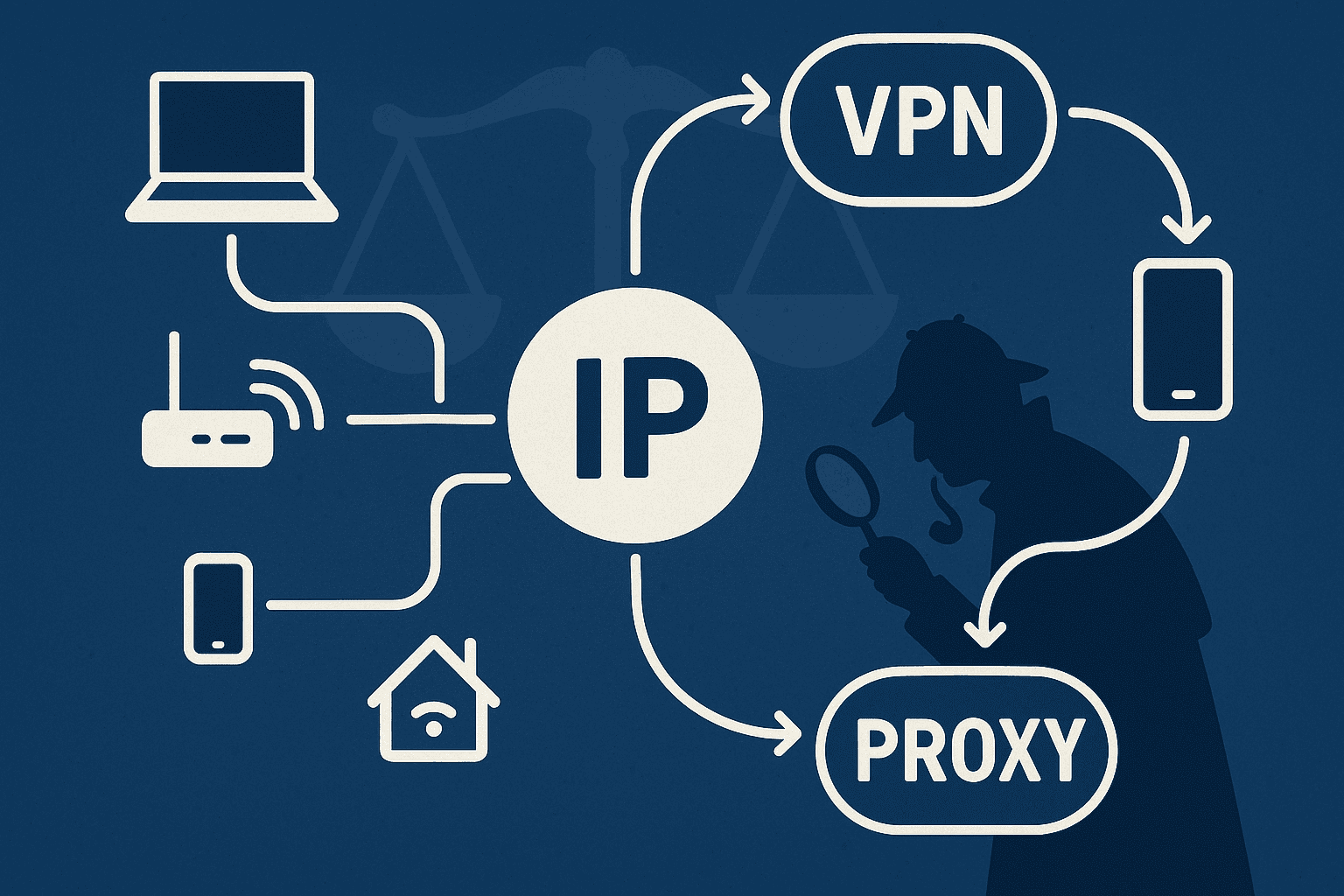
Network forensics
Uncategorized
Windows forensics
Don't miss out on expert insights!
Subscribe to our blog for digital forensics knowledge that may impact your case.